Unggulan
- Dapatkan link
- Aplikasi Lainnya
"how Do Criminals Often Attempt To Avoid Detection In The First Stage Of
The idea of money laundering is essential to be understood for these working within the financial sector. It's a course of by which dirty money is transformed into clean money. The sources of the cash in precise are legal and the money is invested in a means that makes it look like clean money and conceal the identity of the legal a part of the cash earned.
While executing the monetary transactions and establishing relationship with the new prospects or sustaining current prospects the duty of adopting sufficient measures lie on each one who is part of the organization. The identification of such element at first is straightforward to deal with as a substitute realizing and encountering such conditions in a while within the transaction stage. The central financial institution in any nation offers full guides to AML and CFT to fight such actions. These polices when adopted and exercised by banks religiously provide enough security to the banks to deter such situations.
Criminal event stage Most transfer of physical evidence. They dont want to get caught and will stop at nothing to avoid getting caught.
Pdf Reasons For Gaps In Crime Reporting The Case Of White Collar Criminals Investigated By Private Fraud Examiners In Norway
Theres generally two kinds of cracking available.

"how do criminals often attempt to avoid detection in the first stage of. For example a drug dealer in another country depositing cash from his illegal trade into a local bank. The first step is to do a thorough review of the suspects history. The stages of money laundering include the.
There are plenty of tools like Aircrack-ng John The Ripper and DaveGrohl that attempt to brute force passwords. Cybercriminals are resourceful when deceiving users by crafting content and evading detection patterns customization of content copy of. Reason to justify changes to criminal lawdeterrence.
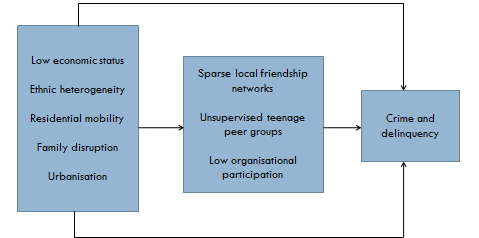
When attempts at denial do not succeed a guilty suspect often makes objections to support a claim of innocence eg I would never do that because I love my job The investigator should generally accept these objections as if they were truthful rather than arguing with the suspect and use the objections to further develop the theme. A chart showing what happens at the different originating stages of evidence. The rise of online banking institutions anonymous online payment.
The use of the Internet allows money launderers to easily avoid detection. They mislead police stage crime scenes and destroy evidence. And b it places the money into the legitimate.
The originating stages of evidence long description. For example criminals may structure cash deposits to avoid threshold reporting requirements or seek out complicit merchants who will accept their illicit proceeds without reporting the. Placement layering and integration-aka hide move and invest Placement.
This is done so that they can get rid of the cash that is derived from criminal sources. The three stages are. Many people point to the need to deter criminal actions after a high-profile incident in which an offender is seen to have received a light.
Refers to the initial point of entry for funds derived from criminal activities into the financial system. This might mean wiping files and metadata overwriting data with false timestamps timestomping and misleading information or modifying critical information so that it looks like the data was never touched. Cyber-attackers do the same thing.
A it relieves the criminal of holding and guarding large amounts of bulky of cash. The modus operandi or method used by a criminal to commit an offense sometimes helps to identify the suspect as many offenders repeatedly commit offenses in similar ways. Mental illness doesnt develop overnight so its important to know if the person has been hospitalized or treated for.
Child molesters who groom often do so while keeping a guise of being kind charming and helpful van Dam 2001. Phishing is so successful today since users are experiencing an infobesity through their received emails making them less cautious to detect phishing attempts. A burglars method of entry into a house the type of property stolen or the kind of deception practiced on the victim of a fraud all may suggest who was responsible for a crime.
Sexual abuse can be more easily committed without detection van Dam 2006. Placement The first stage of money laundering is when the individual participating in criminal activity places cash proceeds into the financial system. The first is some form of dictionary attack so called because the attacker just.
Conceal their presence and mask activity to avoid detection and thwart the inevitable investigation. Money laundering is often comprised of a number of stages including. There is often no attempt to move or otherwise conceal the corpse after the murder.
The placement stage represents the initial entry of the dirty cash or proceeds of crime into the financial system. Deterrence is the theory that criminal penalties do not just punish violators but also discourage other people from committing similar offenses. Money laundering is often described as occurring in three stages.
They strategically manipulate the victim their family and the community to hide their deviant intentions and avoid detection. Generally this stage serves two purposes. Post-crime stage Avoiding apprehension.
Disorganized criminals may be young under the influence of alcohol or drugs or mentally ill.

Media Construction Of Crime Revisited Media Types Consumer Contexts And Frames Of Crime And Justice Baranauskas 2018 Criminology Wiley Online Library

The Presumption Of Innocence And The Media Coverage Of Criminal Cases Arisa

Pdf Gearing Up Against Crime A Dynamic Framework To Help Designers Keep Up With The Adaptive Criminal In A Changing World

Anatomy Of A Ransomware Attack Cryptolocker Cryptowall And How To Stay Safe Infographic Cyber Security Awareness Computer Security Computer Science

The Presumption Of Innocence And The Media Coverage Of Criminal Cases Arisa
5 The Crime Prevention Effects Of Incarceration The Growth Of Incarceration In The United States Exploring Causes And Consequences The National Academies Press
5 Proposed Classification Of Crime For Statistical Purposes Modernizing Crime Statistics Report 1 Defining And Classifying Crime The National Academies Press

What To Do If You Re Being Investigated For A Criminal Offence In Singapore Singaporelegaladvice Com
Crime Prevention Criminal Justice Module 2 Exercises
Evaluating Criminal Transactional Methods In Cyberspace As Understood In An International Context Crimrxiv
Pdf A Study On The Model Of Fact Finding In Criminal Investigation
Crime Prevention Criminal Justice Module 2 Key Issues 2a Detailed Explanation Of Tonry And Farrington S Typology
Https Www Ijicc Net Images Vol7iss8 7823 Kriti 2019 E R Pdf
Pdf Reducing And Preventing Organised Crime An Evidence Based Critique Special Issue Evidence Based Approaches To Regulating Organized Crime Guest Editor Michael Levi
The world of laws can seem to be a bowl of alphabet soup at times. US money laundering regulations aren't any exception. We've got compiled an inventory of the top ten money laundering acronyms and their definitions. TMP Risk is consulting firm centered on defending financial companies by lowering threat, fraud and losses. Now we have big financial institution experience in operational and regulatory risk. We have now a robust background in program management, regulatory and operational danger as well as Lean Six Sigma and Business Course of Outsourcing.
Thus money laundering brings many hostile penalties to the group due to the dangers it presents. It will increase the probability of major risks and the opportunity cost of the bank and finally causes the bank to face losses.
Postingan Populer
How Long Does It Take For Mold To Grow
- Dapatkan link
- Aplikasi Lainnya
What Are Money Laundering Typologies
- Dapatkan link
- Aplikasi Lainnya
Komentar
Posting Komentar